The Good, the Bad, and the Ugly Use of IoT: Who Owns the Data?
Supply chain management and the IoT
“We have the Internet on toothbrushes now, and it’s kind of dumb.” Thus spoke Peter Vanderminden, a widely recognized thought leader on IoT and digital supply chain, during a lively presentation at a recent Predix meetup.
As supply chain management (SCM) is one of his major interests, Peter discussed the use of analytics in this realm. He noted that in recent years, quality improvement programs—such as Lean, Six Sigma, and Total Quality Management (TQM)—had had the effect of reducing defects and the need for service engagement with customers.
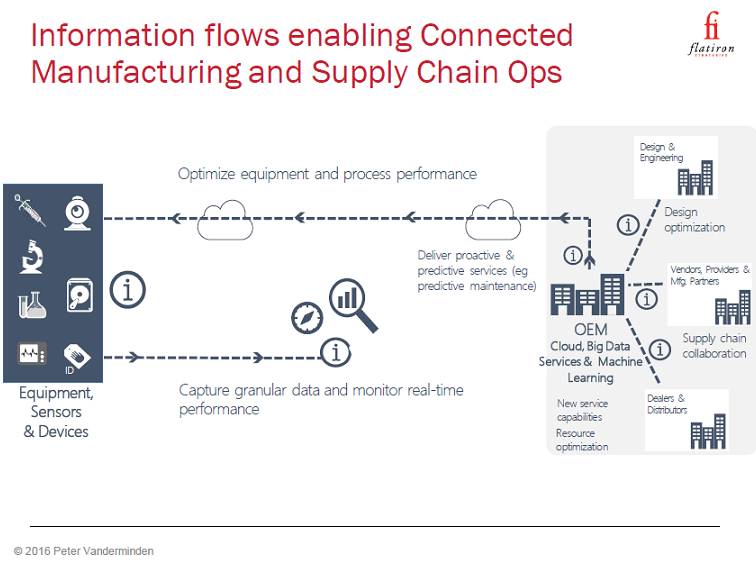
Integrating IoT engagement, specifically with data telemetry throughout the supply chain, is a next step. Here’s how it can improve the manufacturing process:
“Information flows enable connected manufacturing and supply-chain operations.”
—Peter Vanderminden, Flatiron Strategies
The challenges when undergoing transformation
However, in a sector where the literal turning of very large ships is commonplace, companies will face a host of obstacles that are not easily addressed, Peter said, including:
- Adopting new business models
- Adopting new technology
- Learning to become a software company (editor’s note: something so many industries face)
- Learning to become a hardware company
- Industry partnering, coopetition is often required
- There is high risk of making mistakes to meet customer service-level engagements (SLEs)
- May try to monetize the wrong aspects
- Tendency to focus on the direct vs. indirect models
- Questions over who owns the telemetry data?
- Challenges concerning security, privacy, and transparency
- Mismatch of existing skills within the organization
The good IoT practices
Peter then took attendees through a “good, bad, and ugly” tour of the use of IoT within SCM implementations around the world. The SCM software generates more than $10 billion in annual revenue, according to Gartner. SCM itself is the critical linchpin in moving goods to keep the global $75 trillion economy.
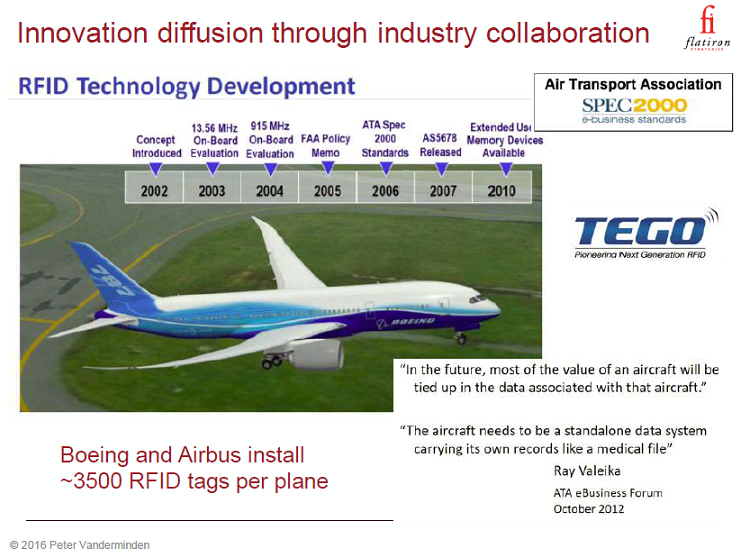
Peter’s focus on good IoT deployments carried a theme of “innovation diffusion through industry collaboration.”
It included a look at the “flying parts” program developed by Tego and deployed on airliners from Boeing and Airbus. The planes have around 3,500 parts with RFID tags, thereby providing instant information during inspections and saving large amounts of maintenance time. It’s important to note that this concept was first outlined in 2002, with initial test deployments in 2010. Patience is a virtue when doing complex work such as this.
(Note: Our company is also involved in a collaborative testbed that relies on RFID tags for better baggage tracking within airlines.)
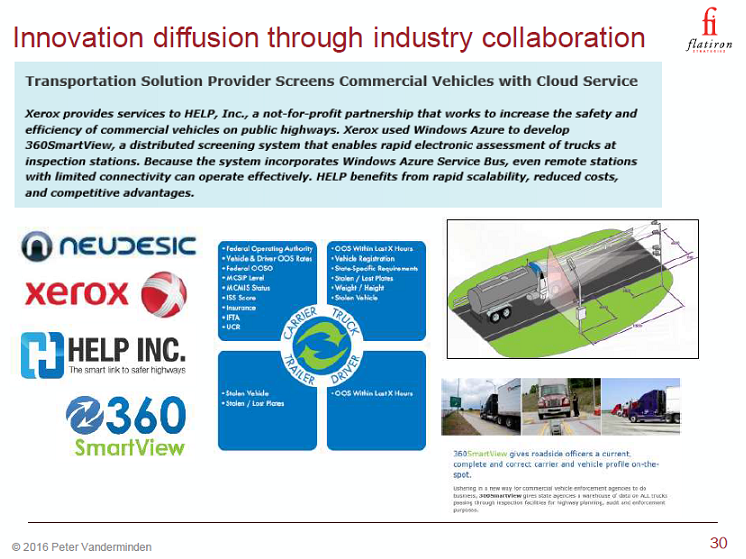
Another good project is a distributed screening system for commercial trucks. Rapid assessments are made at inspection stations with a solution created by Xerox and based on Microsoft Azure.
Michelin offers another good example, with an innovative billing program for the giant tires used on big mining machines. Michelin “takes over management of all aspects of the tire performance,” according to Peter. “A unique metric called ‘ton-kilometer’ is then employed, quantifying the tire contribution to the overall performance of the machine.” The new data about productivity improvements is then shared among all parties, including the mine’s operators.
The bad IoT practices
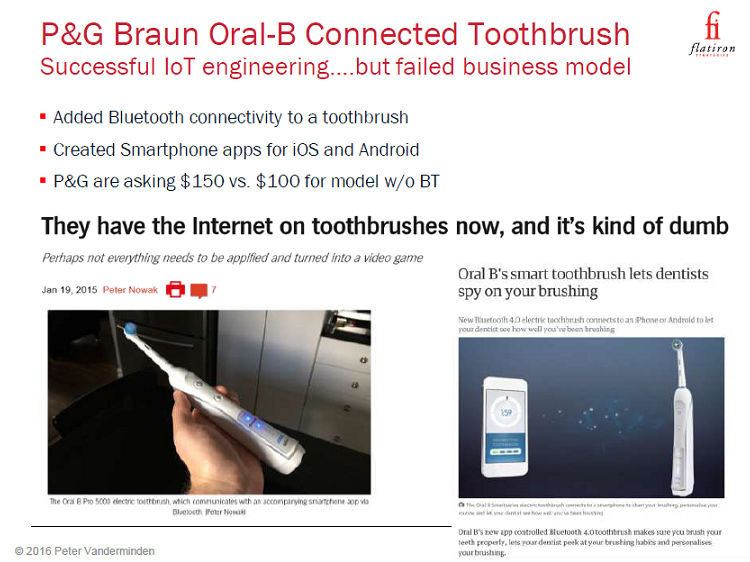
A less good (i.e., “bad”) example of the IoT in action comes from P&G Braun Oral-B toothbrush, Peter said. Replete with Bluetooth connectivity and smartphone apps, the toothbrush can be had for only $150, and “lets dentists spy on your brushing,” Peter noted.
“Perhaps not everything needs to be turned into a video game.” —Peter Vanderminden
Custom coffee machine manufacturer Keurig also garnered Peter’s scorn, with its attempted use of Digital Rights Management (DRM) and connectivity to protect its units uniqueness once its original patents expired.
Other bad IoT examples were offered up from:
- John Deere, which invokes the Digital Millennium Copyright Act (DMCA) to claim tractor owners don’t really own their own tractors (similar to the way Microsoft for years claimed you didn’t really own your own software).
- Tesla, which secretly updates its customers’ cars.
- Uber and its “God View” tracking tool used to follow a pesky journalist.
The ugly IoT practices
Then cometh the ugly. Peter’s first example was that of a secret spying program by New York’s E-ZPass on untolled roads, elegantly executed with the stylish units shown in the picture below:
Peter also described:
- a Smart City program (also in New York) that carried an ancillary benefit of spying on citizens through information kiosks
- a failed program by Rite-Aid and others to compete with Apple Pay
- an antivirus scan that shut down a medical device in the middle of heart surgery (hate it when that happens)
Who really owns our data?
During his SCM segment, Peter made very good points about the importance of global supply chain management and how smart IoT usage can only serve to make it more efficient.
Despite modern transportation containers, which can quickly be transferred from ship to train and train to truck, even small, incremental increases in efficiencies can save large amounts of time and money. Worldwide port congestion remains an issue and the IoT can address this issue by balancing port capacity with more consistent ship arrivals.
Peter then discussed the large, important issues buried within the elegance and the tomfoolery. Who really owns the data created by IoT deployments? Where are the lines (if any) drawn concerning surveillance and that quaint word “privacy”? What role will (and should) regulators play?
Thus, Peter examplified how great tools in inept hands can hurt the reputation of an entire class of technology. This is the case with some of these early IoT/analytics efforts. Its particularly concerning to see government agencies being obsessed with spying on their own constituents, with so many corporations aping this activity.
Regulatory answers to this problem are usually not the answer, as we end up with one set of government regulators trying to regulate another set of government regulators. EU law, something not mentioned in this presentation, is much stricter than the US law when it comes to privacy, often making it difficult for the US companies to do business in much of Europe. Yet European governments also like to “surveil” their people in the name of security and related issues.
So, what can be done? How can software development communities and hardware developers throughout the world actively oppose the “bad” and especially the “ugly” uses of the IoT and the technologies it encompasses, while encouraging the “good”?
Related reading
- IoT for Airlines: Smart Baggage Tracking with RFID Tags and Cloud Foundry
- Cybersecurity for the IoT: Issues, Challenges, and Solutions
- SF State University Is Working on IoT-Driven Watering to Fight Droughts
- The Impact of IoT on the Economy and Business Models
- Bringing Healthcare Home with the IoT
Want details? Watch the slides!
About the expert