Cloud Foundry and IoT Concerns: The Need for Standardization and Transaction Authentication
The abundance of IoT devices challenges the standardizing of their management for Cloud Foundry use. Currently, different companies have to be assigned to deal with different fields of operation—one for telecommunications, one for healthcare, one for agriculture, etc. This blog post explores the issue, figuring out possible solutions.
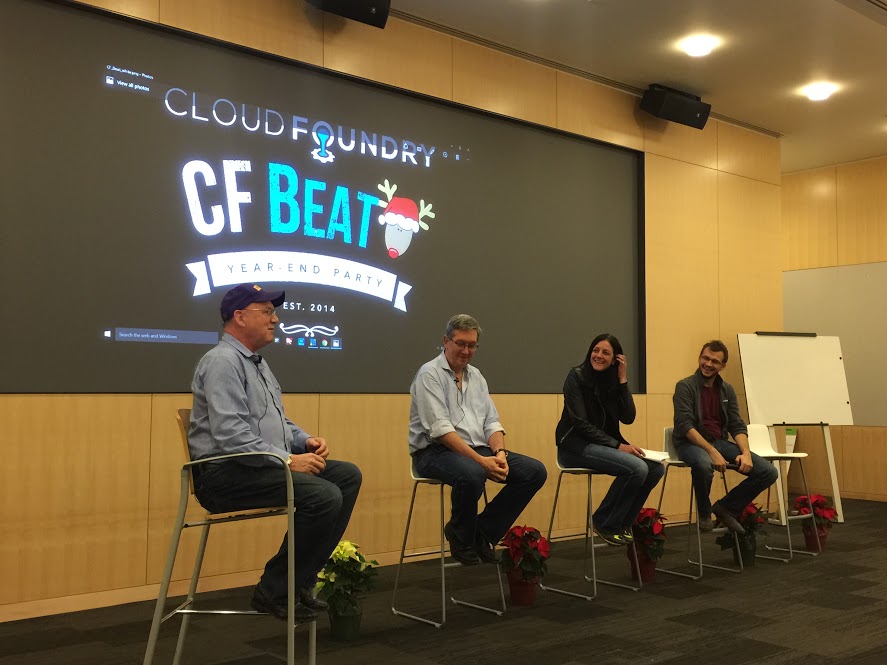
During the last Cloud Foundry Beat panel discussion on “Is Cloud Foundry the Ultimate IoT Machine?” Momenta Partners’ Strategic Advisor, , expressed her concerns on standardization and security for Cloud Foundry and its connection with the Internet of Things.
“From a Cloud Foundry perspective, if you take apart the IoT stack and start thinking about what services are common across any IoT in communication, everybody will need device management,” Laura says. “Right now, everybody is acquiring device management companies, so you have all these different permutations of device management, but the reality is that there’s a bunch of endpoints and there’s a bunch of devices that need to be managed.”
Standardization negates the need for multiple providers
She further details that as it is now, you would need different companies to manage devices assigned in different fields of operation—one for telecommunications, one for healthcare, one for agriculture, one for manufacturing, and so on. Simply put, device management needs to be standardized to promote ease of use for the end-user.
“You can go to Jasper if you want telecommunications or you could go to OSIsoft if you want manufacturing but is there a way to standardize this set of services for being able to have device management?” questions Laura.
The current situation is analogous to having different contact numbers for varying household emergency services like the fire department, the police department, the hospital, and the like. Having all these services centralized on one number is be the same goal for device management standardization.
The need for authenticating each transaction
Apart from device management standardization, she also voiced concerns about security, not just for data, but most especially the authentication of transactions.
“One of the challenges is around security, that is, the security from the authentication of a transaction,” adds Laura.
As an example, she poses, “If I am making a transaction out of an oil rig, you don’t actually want the transaction back to the oil rig to come from some unknown place. You have to authenticate the transaction on the way back because that’s invoking an action on the oil rig and that needs security.”
She continues on to explain how the lack of transaction authentication security in the oil rig scenario could lead to possibly devastating consequences. “The data out of the oil rig, sure, you want that to be secure, but it’s more you don’t want anyone to have a transaction that brings down a power grid or explodes the oil rig.”
Lack of authentication: a possible solution
Putting the grimness of exploding oil rigs and shutting down power grids behind us, Laura concludes that Cloud Foundry may be the ideal solution for addressing her two key concerns. She also suggests a method for fixing at least one of the problems which stemmed from an earlier discussion.
“Those are the types of things that I think most standardization and applications would be interesting for Cloud Foundry and there are ways to do it,” explains Laura. “You talk about a block chain for financial services. There’s opportunities to block chain relative to IoT for authentication of a transaction.”
To clarify, block chains, made popular by the Bitcoin protocol, are permissionless distributed databases that house ever expanding records of data that are protected against any form of modification and tampering even from the administrators that monitor the block chains themselves.
Whether or not her suggested solution can be put to actual use, the concerns she identified on device management standardization and transaction authentication remain valid and they leave an opening for Cloud Foundry to step in and put things in order.
Want more details? Watch the full video!
Table of contents
|
About the speaker