Evaluating Pivotal Container Service for Kubernetes Clusters
General availability of the service
Last week, Pivotal has announced general availability of Pivotal Container Service (PKS). The service aims at enabling operators to deploy, run, and provision enterprise-grade Kubernetes clusters. At the moment, PKS v1.0 provides support for Google Cloud Platform (GCP) and VMware vSphere.
As the service was launched, our engineers tried it out to see what’s in there from a user perspective. Here, we share our findings related to the ease of installation, functionality, security, supported integrations, and available documentation.
Evaluation
Installation
One can download the PKS release v1.0 here. For Pivotal CF, it is recommended to install PKS on a separate instance of Ops Manager v2.0 to ensure better security. However, it means that operators will have to manage a number of separate environments—thus increasing operational expenses.
 Image credit
Image credit
Configuration
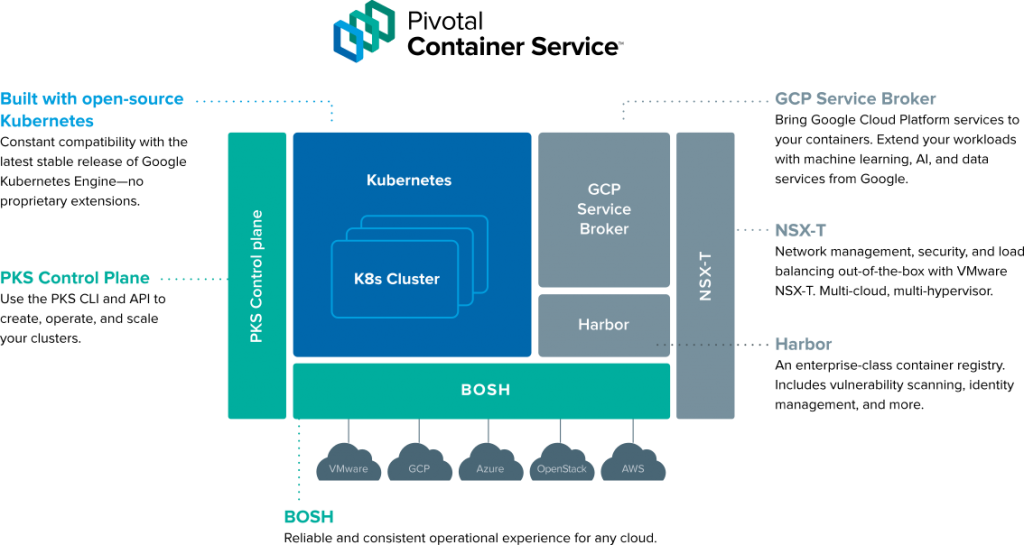
To create a PKS instance on Google Cloud Platform, an operator manually sets up and configures load balancing. This is needed to connect to PKS API—responsible for deploying Kubernetes clusters. Then, an operator has to set up another load balancer to establish traffic routing to a Kubernetes cluster.
In case of VMware vSphere, the configuration of load balancing is automated through the integrated NSX-T solution, which manages traffic routing via the Network Address Translation.
 The PKS architecture (Image credit)
The PKS architecture (Image credit)By default, PKS offers three templates for service plan configuration. Still, these templates are not predefined, so an operator has to manually assign resources for Kubernetes clusters. Usually, such templates are already predefined based on average amount of resources needed for “small,” “medium,” or “large” deployments. With manual resource assignment, an operator relies on his/her experience and intuition solely, so there may be either insufficient or abundant resources.
Network management and security
Using NSX-T, PKS allows for managing software-defined virtual networks and ensures the security of the Kubernetes network. Being purely a vSphere’s component, NSX-T is not available for Google Cloud Platform, though one may employ Flannel for GCP as an option.
PKS is integrated with Harbour—an enterprise-grade container registry that enables vulnerability scanning, identity management, activity auditing, etc.
Unlike Cloud Foundry, PKS UAA features only two access roles, called scopes:
pks.clusters.admin—users with this scope have full access to all the clusters.pks.clusters.manage—users with this scope can only access clusters that they’ve created.
We shot a video on creating and managing users in PKS UAA via UAA CLI.
On-demand provisioning
To provision the deployed Kubernetes clusters, an operator uses BOSH, which is really awesome to those accustomed working with the tool.
Command-line interface
With the PKS service, an operator makes use of the three command-line interfaces (CLI).
PKS CLI and BOSH CLI are utilized to create and configure clusters, while kubectl provides a native command-line interface to Kubernetes for further cluster management.
Below, you find a video—created by our team—on how to use PKS CLI to get cluster credentials.
Supported integrations
Apart from NSX-T and Harbour, PKS is also integrated with vRealize Operations Manager, vRealize Log Insights, and Wavefront to enable a fully fledged on-prem deployment for VMware vSphere.
PKS supports CredHub to manage credential generation, storage, and access in secure manner. It is also possible to use Helm, a package manager, for Kubernetes apps running on Pivotal Container Service.
Documentation
Pivotal Container Service is well-documented, featuring instructions on installation, management, diagnosing, and troubleshooting. The official documentation can be found here.
Conclusion
Pivotal Container Service gives an outstanding opportunity for enterprises to evaluate Kubernetes as a runtime for the developed applications, as well as facilitates cluster management for operators already using Kubernetes. We are looking forward to the upcoming releases, which hopefully will bring in improved automation, support for more IaaS systems, and native integration with open-source Cloud Foundry.
Further reading
- K8s Meets PCF: Pivotal Container Service from Different Perspectives
- Kubo Enables Kubernetes Environments Managed by Cloud Foundry’s BOSH








